Description
Display TCP flows like tcpdump. Features are connection or flow highlighting (up to 256 colors for supported terminals like rxvt-unicode-256color) or powerful matching capabilities.
Options
-i CONNECTIONS, --connection-id=CONNECTIONS specify the number of displayed ID's -d DIFFERENTIATE, --differentiate=DIFFERENTIATE specify if "connection" or "flow" should be colored -m MATCH, --match=MATCH if statment is true the string is color in red -s, --suppress don't display other packets -n, --number number the packets
Usage
Highlight different connections or different flows. If several connections are captured then the connection options provide a quick way to see how many connections are captured and when. If one flow is captured then this is a method to see TX and RX directions of the flow. Used to highlight only packets there the provided filter evaluate to true. Filter can be: Only useful in combination with match. Instead of coloring packets red (which is the default), only matched packets are displayed. All other packets are not displayed. Show in first row the absolute packet number. This can be used to correlate one packet with the packet in wireshark or tcpdump.
Examples
Highlight different flows
$ captcp show -d flow capture.pcap
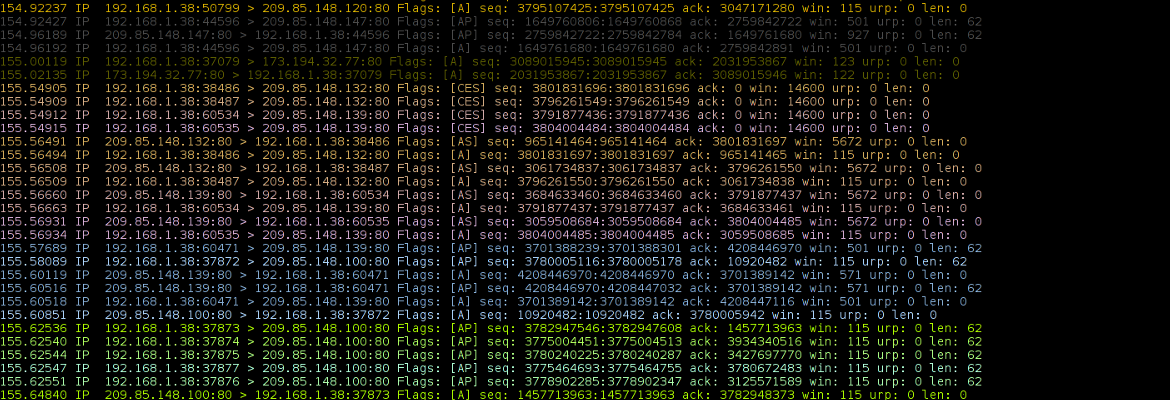
The next example and image illustrate the default options to differentiate connections.
$ captcp show capture.pcapimage::images/show-connections.png
Matching can be really powerfull. We start with the hello world example:
$ captcp show --match True trace.pcap
This will match all packets, thus all packets are red colored. Another usefull option is --suppress: only packets are displayed where the match evalutated to true. This can be used to count special packets. As an example: to display only packets with TCP SACK (selective acknowledgements) you can filter for it and suppress all other packets
$ captcp show --match "sackblocks" --suppress trace.pcap
Highlight packet where the TCP SYN and ACK flag is set:
$ captcp show --match "syn_flag and ack_flag" trace.pcap
Show packets where the Maximum Segment Size is less then 1000:
$ captcp show --match "mss and mss < 1000" trace.pcap
It is important to note that MSS must be checked before the values can be compared. A packet where no MSS is present (the MSS option is only set at the Three Way Handshake) the mss value is False. So a plain statement like "mss < 1400" will evalulate to "False < 100" which is true in Python. Therefore the additional check is required.
Show all packets with SACK blocks and where the first TCP SACK block (left-edge) starts with a number less then the acknowledgenumber. Normally this is not superfluous, but sometimes DUP-ACKs are cached and retransmitted and the SACK information is not updated.
$ captcp show -m "sackblocks and len(sackblocks) > 0 and sackblocks[0][0] < ack" --suppress --number trace2.pcap
The following match keywords are valid and can be used
| Keyword | Description | Type | Example |
|---|---|---|---|
| sip | Source IP address, IPv4 or IPv6 | str | sip == "192.168.0.1" or sip == "192.168.0.2" |
| dip | Destination IP address, IPv4 or IPv6 | str | re.search( r'192\.168.*', dip) and re.search( r'.*\.2$', dip) |
| seq | TCP Sequence Number | int | seq > 23233 |
| ack | TCP Acknowledgement number | int | ack > 1000 |
| urp | TCP Urgend Data pointer | int | urp == 1000000 |
| sum | TCP Checksum | int | sum != 0 |
| sport | TCP Source Port | int | sport == 80 and dport != 80 |
| dport | TCP Destination Port | int | dport in (80, 443) or dport in range(1000, 2000) |
| ack_flag | Acknowledgement Flag | bool | ack_flag == False |
| syn_flag | Synchronization Flag | bool | ack_flag and syn_flag |
| urg_flag | Urgend Pointer Flag | bool | urg_flag == True and ack_flag |
| psh_flag | Push Flag | bool | psh_flag and not ack_flag |
| fin_flag | FIN Flag, Type | bool | syn_flag and fin_flag |
| rst_flag | Reset Flag | bool | rst_flag and not fin_flag |
| ece_flag | ECE (ECN) Flag | bool | ece_flag and cwr_flag |
| cwr_flag | CWR Flag | bool | not cwr_flag |
| mss | Maximum Segement Size (MSS) | int | mss < 1400 |
| wsc | Window Scaled Option | int | wsc == 0 |
| tsval | TCP Timestamp TSVAL value | int | tsval == 0 and tsecr == 0 |
| tsecr | TCP Timestamp TSECR value | int | tsval != 0 and tsecr != 0 |
| sackok | Selective Acknowledgements OK flag, Used during Three Way Handshake | bool | sackok |
| sackblocks | If SACK is transmitted | list of list | sackblocks and len(sackblocks) &tg; 2 |